Ransomware attacks are on the rise.
Approximately $350 million in ransom was paid to threat agents in 2020. That’s more than a 300% increase from 2019. There have already been multiple, notable ransomware attacks in 2021, with global ransomware costs expected to reach $20 billion this year.
The attacks are more sophisticated. At one time, they were just phishing emails deploying malware software to encrypt servers and offering decryption keys in exchange for a six-figure ransom.
Now, they are deploying malware software to encrypt business systems and target backup systems and sensitive data. Those are being held hostage for payment in the mid- to high seven-figure range, reaching tens of millions of dollars.

4 Impacts of Ransomware Attacks
The average ransom payment during the first quarter of 2021 was $220,298, up from $154,108 during the last quarter of 2020. As more organizations pay ransoms, there are more resources available to attackers, increasing their attack rate and the severity of their attacks.
Ransomware, however, cost organizations more than money. The impact of a ransomware attack includes several business liabilities.
1. Loss of Valuable Data
Many organizations affected by ransomware attacks eventually regain access to their data. Yet, some of that data is lost, because of decryption errors and data corruption. Of the organizations that paid a ransom, 92% didn’t get back all their data. And 29% couldn’t recover more than half the encrypted data.
2. Business Disruption and Loss of Revenue
If you don’t have access to the data needed to run your business, your business operations will suffer.
Your employees need access to business-critical applications and data to generate revenue. Customer access to your products or services is needed to generate sales revenue.
Any downtime severely impacts your revenue through lost opportunities, service outages, production shortages, and more. The average downtime following a ransomware attack is 23 days. The average cost to organizations from downtime is $762,231.
3. Liability and Compliance Costs
If your sensitive data is breached or exposed, your organization may need to handle litigation costs, fines and identity monitoring to compensate users whose data was lost or stolen. Organizations following regulations governing the protection and use of data could incur steep penalties and regulatory fines for noncompliance.
4. Compromised Customer Confidence and Brand
The damage to your organization’s reputation is difficult to avoid. No matter how fast and professionally you can respond to and remediate a ransomware attack incident.
If sensitive data is compromised, the confidence of your customers, partners and investors is diminished. Customers and partners have little patience for breaches, with 59% of them avoiding doing business with an organization following a breach. And 66% turn to your competitor, if systems and applications aren’t restored within three days after a ransomware attack.

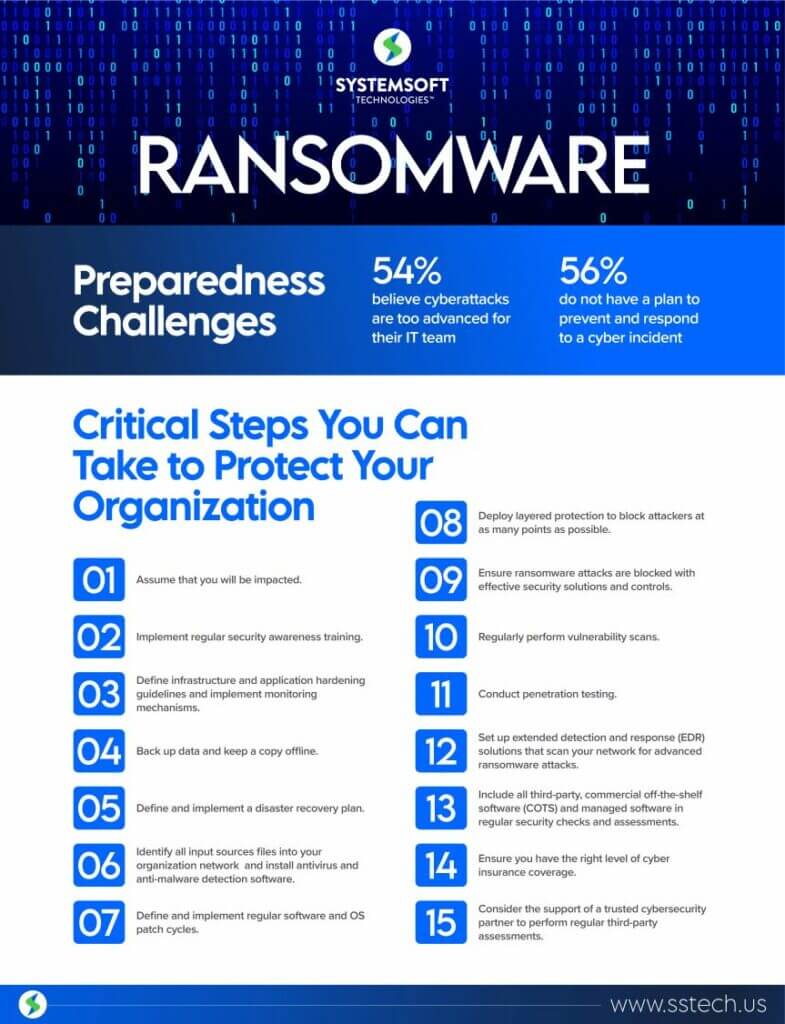
Preparedness Challenges Against Ransomware Attacks
According to a recent McAfee Cybercrime report, 56% of surveyed organizations said they don’t have a ransomware solution to both prevent and respond to a cyber incident. Out of the 951 organizations with a response plan, only 32% said the plan was effective. More than half of respondents believe cyber attacks are too advanced for their IT team to handle without help.
The increase in ransomware attacks, though, isn’t because organizations don’t have the right people and processes in place. Today’s complex infrastructure of microservices, cloud platforms, containerized architectures and distributed applications add to the challenges of IT security teams to defend and protect infrastructures.
Ransomware attackers have grown adept at sniffing out and taking advantage of system vulnerabilities.
Therefore, ensuring you have a strong security posture and ransomware solution are critical. Finding blind spots and building a robust security risk management program and incident response plan are essential to protecting your organization’s infrastructure and reputation.
Act
Ransomware has grown into a lucrative multibillion-dollar industry, with most of the ransom shared among highly organized criminal groups. Arresting and bringing these criminals to justice are difficult. They keep becoming more sophisticated and bolder with threats and higher financial demands.
The threat of a ransomware attack isn’t expected to go away anytime soon.
The bottom line: Avoid the impacts of ransomware attacks by putting in place a strong cyber security infrastructure and incident response plan. The response plan considers the impact of the incident across your entire organization, not just the impact to your IT infrastructure.

Protect Your Organization Against Ransomware Attacks
- Assume you will be impacted. It’s better to be prepared with a cyber incident response plan.
- Implement regular security awareness training for all new and existing employees to inform and educate your workforce about how to find and report cyber threats.
- Define infrastructure and application hardening guidelines and implement monitoring mechanisms to stay compliant.
- Back up data (encrypted) and keep a copy offline, using the industry standard approach of 3:2:1 (three sets of backups, using two different media, one of which is kept offline).
- Define and implement a disaster recovery plan, which recovers your data and validates business recovery from backup on a regular basis.
- Identify all input sources files into your organization’s network, which may include email, file servers, share drives, etc. Install antivirus and anti-malware detection software to catch malicious files and enforce proper quarantine mechanisms.
- Designate and carry out regular software and OS patch cycles, ensuring you have built-in alerts to monitor compliance.
- Deploy layered protection to block attackers at as many points as possible.
- Make sure ransomware attacks are blocked with effective security solutions and controls and detected by threat-hunting, using an Intrusion Prevention System (IPS) and Intrusion Detection System (IDS).
- Consider the support of a trusted cyber security company to perform regular third-party assessments, evaluating your network, applications and security posture.
- Regularly perform vulnerability scans to test security controls and system misconfigurations, seeking vulnerabilities.
- Conduct penetration testing to simulate an attack on your network, exploiting vulnerabilities and figuring out security measure improvements.
- Set up extended detection and response (EDR) solutions, which scan your network for advanced ransomware attacks.
- Include all third-party, commercial off-the-shelf software (COTS) and managed software used by your organization during regular security checks and assessments.
- Stay updated with the right level of cyber insurance coverage.
Check out this ransomware attack infographic to better understand and defend against ransomware attacks and avoid ransomware attack demands.
Conclusion
System Soft Technologies is a trusted technology and security partner dedicated to safeguarding your organization’s cyber-resilience and operational health.
Schedule a demo to discover how your organization can benefit from an operation-centric approach to security.
[Watch on-demand LinkedIn Live Event: Ransomware: Critical Steps You Must Take Now to Ensure Your Organization Isn’t the Next Headline]
About the Author: Phani Yalamanchili

Phani Yalamanchili serves as a Cyber Security Specialist at System Soft Technologies. Phani has more than 15 years of industry experience in the Cyber Security Practice, advising customers about cyber strategy, security architecture implementation and policy. He’s a Security Evangelist, who can build security infrastructures from the ground up, improving security postures for organizations in the financial and healthcare industries. He also can enable DevSecOps practices, embedding security controls within the software delivery lifecycle.
